We all have the expectation that it will never happen to us - until it does. And then what?
I was listening to a podcast last week, and the host was discussing a study that examined caffeine's effects on sleep and alertness. The expectation was that they would find that caffeine was a significant cause of sleep problems. However, when they analysed the results, they found something much more interesting.
The outcome was that the belief that you are drinking caffeinated coffee (even if you're not) can have a stronger effect on your alertness than actually consuming caffeine without being informed.
Our ability to form opinions that affect our lives is something that has fascinated the medical world with the concepts of placebo and nocebo. The question is: why am I talking about this in an article about cybersecurity?
Good question. The answer is that I have noticed over the years that people get very animated about security, and not in a positive way. Often, we have to roll out security in a very “softly, softly “approach to avoid triggering some customers into pulling the rug on security completely. Granted, they are running a business so we need to be cognisant of that, and not play fast and loose with productivity, but I do wonder at times if people are more afraid of security improvements than is necessary. Or perhaps, they are not nearly afraid enough of what a nefarious individual can do if they get past your security defences.
Today, I am reading an article about how AT&T is being sued in some of the largest data breach litigation the US has ever seen. Last week, I was listening to a conference session on quadruple extortion. This is where the bad guys encrypt your data so your company can’t function and ask for a ransom. If you don’t pay, they have also taken a copy of your data, so they threaten to release it on the web. If you don’t pay at that point, they release it on the web and contact your customers. They tell your customers that they offered not to put the data on the web for a fee and that you cared so little about them that you would rather have the money than protect their data. The hackers then ask that client to contact you (their supplier) and impress on you the importance of paying the ransom to remove the data.
To be fair, in my experience, we have not had much/any ransomware so I can see that customers use that recency bias to decide their tolerance/acceptance rate of security protocols. This is a terrible idea though. You are much better off looking at the protocols, asking what the worst-case scenario is for implementation, accepting as much of that risk as possible and cracking on.
If you answer yes to any of the following questions you need to reassess your balance of risk in my opinion.
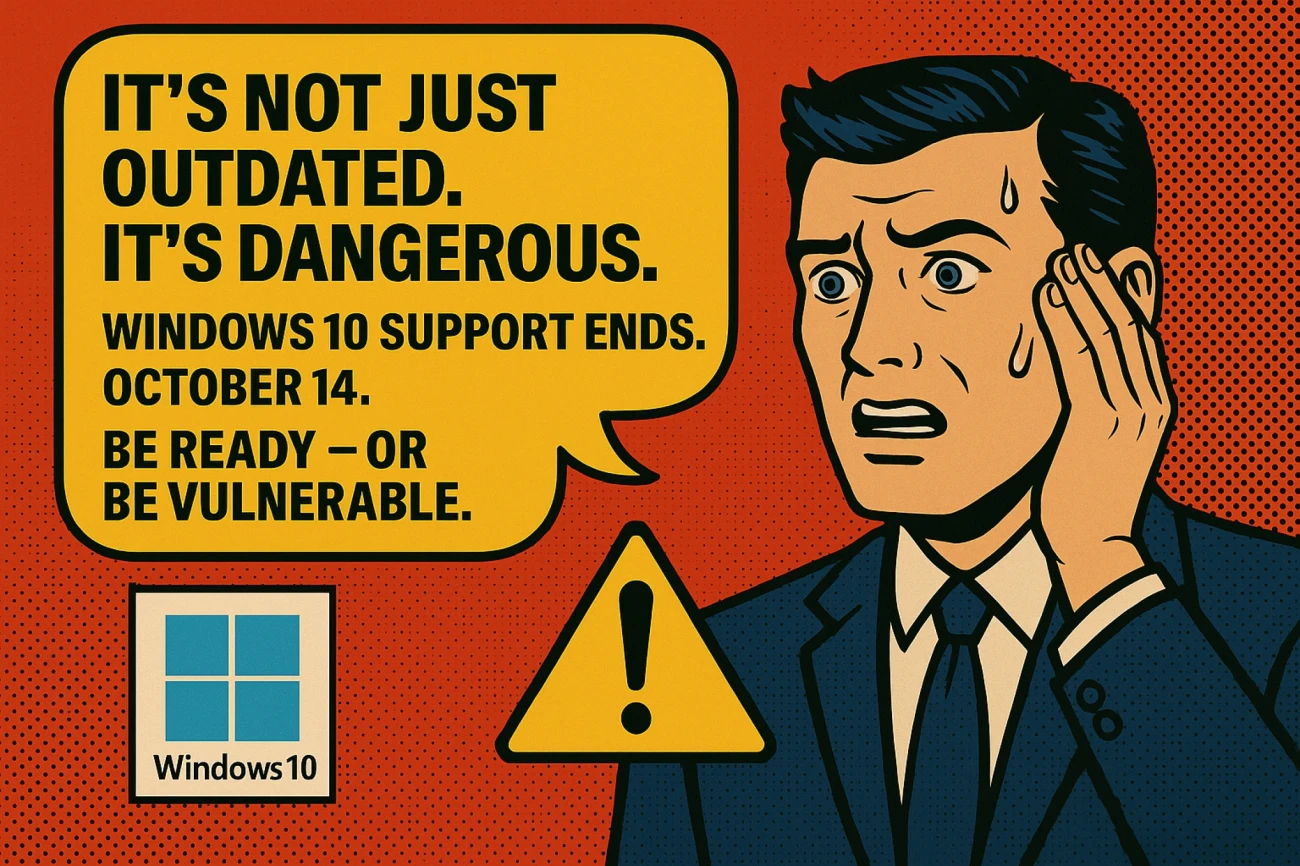
Have you got Windows XP/7/8 and/or Server 2008/2012 in your business? You shouldn’t. These can’t be secured and are a giant open sore on your network.
Do you need to be on a work computer to access resources? This is crucial and you should require this. If you can log on to work from any machine in your home, you will eventually be phished out of your credentials. The level of sophistication in phishing these days means you need a foolproof method and training, while extremely useful, is not it.
Do you have the latest MFA on all users able to log on outside the premises? You should.
Are all your services, like RDS and Citrix, behind a VPN? They should be.
As we like to say, security is a state of mind. With the correct state of mind, you can get a great deal of security implemented.
Maybe it’s time to change your state of mind.
To discuss our security solutions, please get in touch via email or by calling 028 9442 7000.