It's easier now to be hit with a cyber attack from your supply chain than ever before - but you can protect yourself with these 3 steps.
Nihilism; not a good look in IT security.
Given the constant negative information we’re exposed to on IT security, it’s not surprising that discussions around cyber security are more likely to get an eye roll than a “Tell me more!” response.
If Microsoft can be hacked, then what hope does average Joe have? Well, it’s a good question and one with a simple answer. You can have more of an impact than you might think.
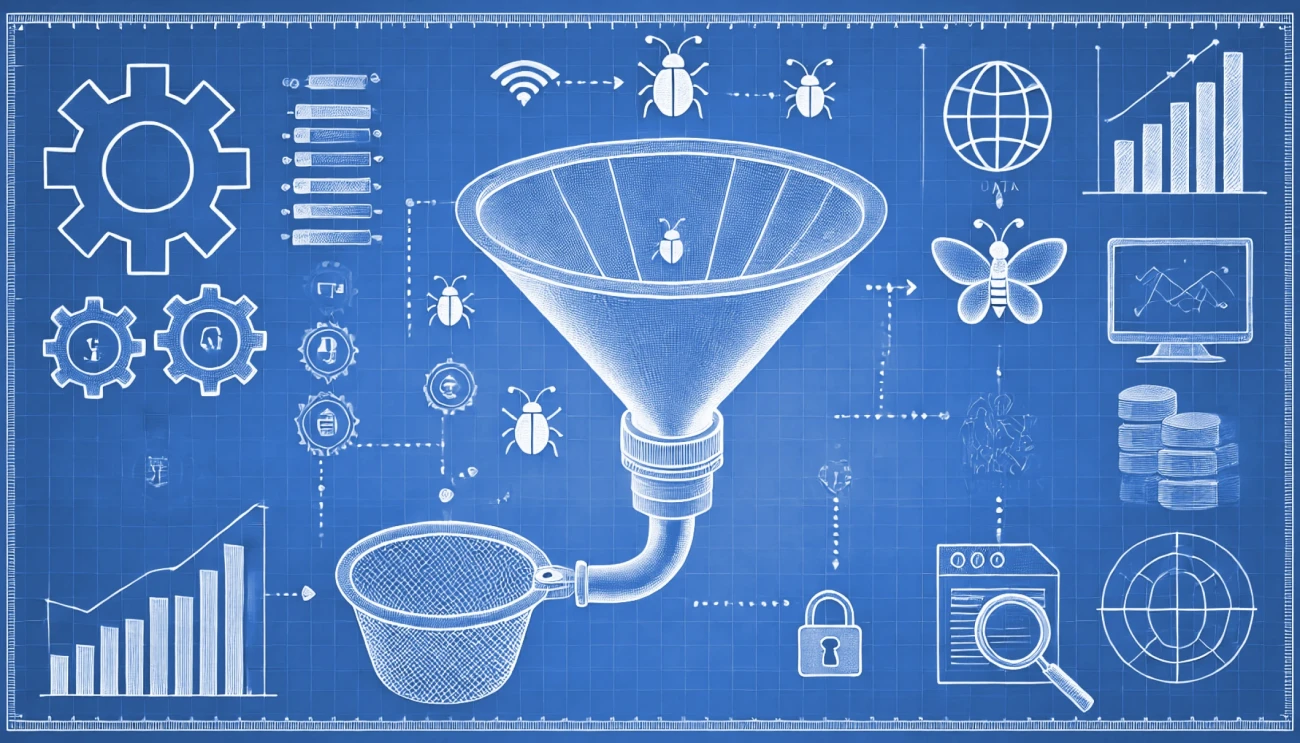
Security Scorecard
At Nitec, we use Security Scorecard to evaluate our, and periodically our customers', security stance. On a recent call with Security Scorecard, they had an insurer present who disclosed their reliance on Security Scorecard to advise on cyber insurance premium levels and coverage eligibility. Security Scorecard had carried out a substantial amount of research to ensure that their latest scores had a high degree of correlation with security breaches, and insurers are taking notice.
The use of Security Scorecard can be very advantageous for customers if you follow the logic:
The largest risks to your security are phishing and ransomware.
Your largest risk for encountering those two attacks comes from the vulnerability of your supply chain.
Having a subscription to Security Scorecard which allows you to examine your own security stance and the third-party risk of your suppliers may allow you to identify the most likely points that supply chain attacks may occur.
Consider this: in 2019, a cyber insurance survey attributed 232 breaches to supply chain attacks. By 2023, this number had skyrocketed to 2,769—a twelve-fold increase, and it makes perfect sense. Most customers have seen the Nigerian prince and the badly spelled Amazon emails, and they have all improved at recognising these threats.
What they're nowhere near as good at spotting though is the instance where a supplier is breached, and the hacker just lurks in the background waiting for a good opportunity to arise. We have seen a significant increase in this ourselves over the last year.
Take this for an example:
A user is compromised in your supplier’s organisation. You send an email to that user asking for an updated quote. A few hours later you get a response to your email with an attachment. You click on the attachment thinking it’s a quote and it’s a PDF of some sort containing a link. It seems a little odd and initially, you are hesitant to click, but you mull it over for a few seconds. After all, you requested this, and the email is a direct reply to the email you sent. This all suggests that it definitely came from 'Barry' at 'A.N. Other Supplier', your trusted contact, so it must be fine. You click the link, and it asks you to sign in to Office 365. Only after you log in and an error appears do you think better of your actions again and call the IT department but by then it’s too late!
Nitec has a few mitigations for this type of attack which are useful to know and understand.
Compliant Device Requirement
This refers to an additional requirement for Office 365 log-ins which requires you to log on from a computer that is owned and managed by the company. This is a very powerful mitigation and stops a substantial number of these attempts dead in their tracks. It's complicated to set up but poses a great deal of extra difficulty for a hacker so it's well worth it. The hacker has your username, password and multi-factor authentication (MFA) token but without a company-owned computer i.e., a compliant device, they can’t get in - disaster averted.
End User Security Awareness Training
Most IT consultants understand that email is an exceptionally insecure form of communication and that's because it was never designed with security in mind. It was designed in universities by researchers with a great degree of trust in colleagues. Whilst some changes have been introduced over the years, (e.g., DMARC), these are not well implemented and largely, leave many users open to abuse by the more nefarious side of the internet via email. IT consultants have a very clear idea of these facts and a very high degree of skepticism of email as a result. End User Security Awareness Training allows you to instill a sense of this mistrust in end users. It also allows you to gauge how susceptible various groups of users are to exploitation. We don’t recommend berating your staff based on the results as often this is counter-productive, but being forewarned is forearmed, and this can be helpful in directing staff training. It can also aid in fulfilling requirements for cyber insurance which often have this security training as a pre-requisite.
A lot of customers are already (wisely) leveraging both of these strategies to reduce their cyber risk. If you're not, take this as your sign to join the club.
If you’re ready to take your security to the next level please get in touch by emailing solutions@nitec.com.