Unlocking the secrets of Cyber Essentials: a tale of Tuckers' breach and how to stay cyber-savvy in today's threat landscape
How does the Information Commissioner’s Office (ICO) see breaches, and what can we learn from one of the more recent cases taken against a victim of a breach by the ICO?
I suppose that when we are the victims of a breach, one might expect some help from the Information Commissioners. In any of our dealings with them on behalf of a few clients and in stories we have heard through the grapevine, they have generally been business–like and quite understanding. However, the latest case against “Tuckers” shows that this understanding has some limits, and it is good to be aware of them.
Tuckers, a firm of solicitors dealing in criminal law, were fined £98,000 for a breach involving losing a client’s confidential data. Almost 1,000,000 files, 60 court case bundles and some special category data were exfiltrated and released on the dark web.
Those of you who are regulars to my musings will know experts suggest that we live in an era of “assumed breach”, so if security experts live in a state of the assumed breach, how can the ICO be throwing around £98K fines when people are breached? The two facts seem to be entirely at odds, you might think.
Alas, no. It is clear that companies and their management teams are expected to take reasonable steps to secure their data, and this was where Tuckers needed to catch up.
There were a few stand–out items worth spending a moment on:
Tuckers had failed to meet the National Cyber Security Centre (NCSC) “Cyber Essentials” standard and knew they did not comply. As the Commissioner put it, the breach was a criminal act that exploited negligent security practices.
Tuckers were accredited to Lexcel, the Legal Practice Quality Mark, which states that legal practices should be accredited to the NCSC Cyber Essentials standard. Still, they had yet to reach that standard.
Further, the Commissioner held that failing to implement Multi–Factor Authentication (MFA) on its remote access systems was negligent. The NCSC has recommended, as of 2018, that all remote access systems be protected with MFA.
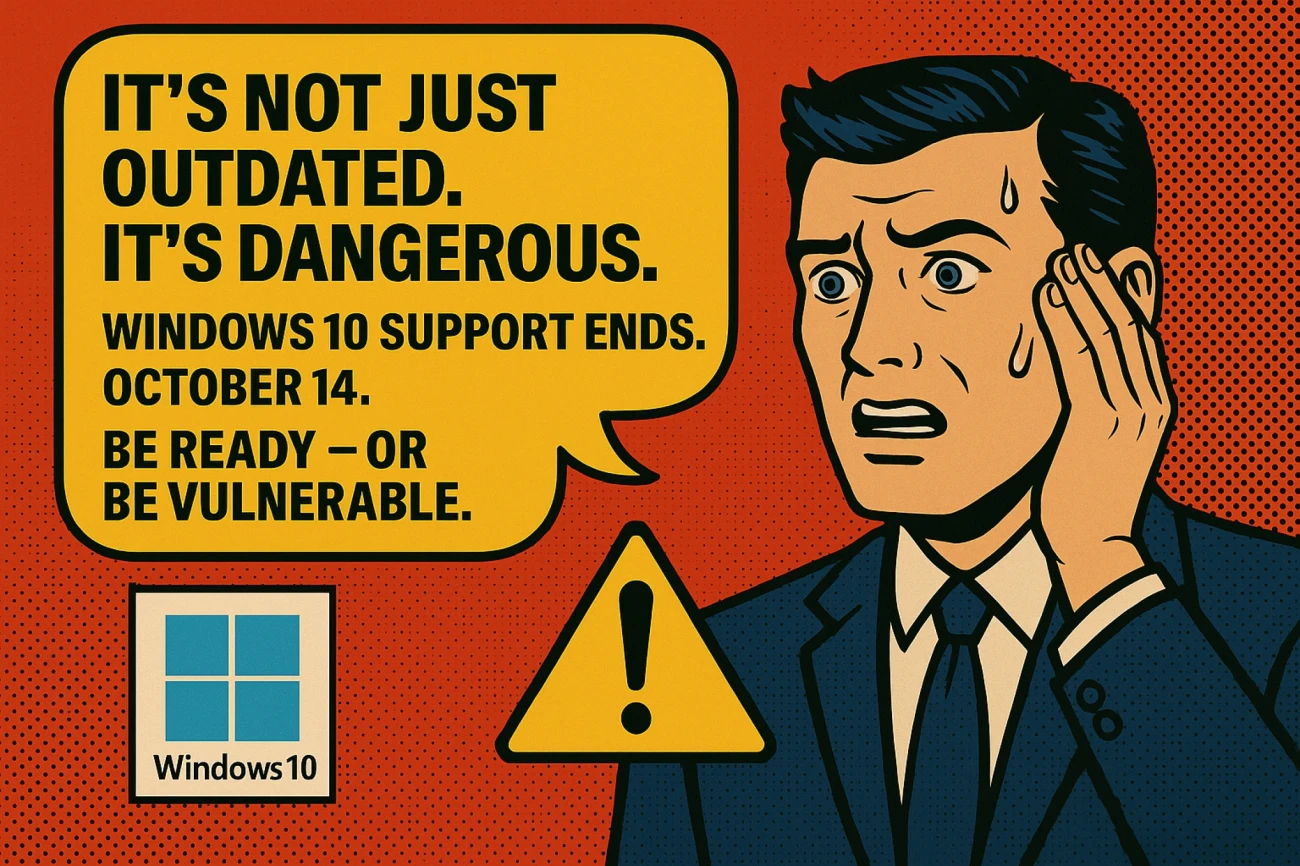
It was considered negligent to continue to use computers that had passed mainstream support and could not receive updates.
Storing data past its 7–year expected life cycle was against retention policies.
I have a feeling I’ll return to this over the next while. Regulars will know that all these items (except maybe the retention) are monitored and displayed in our customer portal. We take all these items very seriously and have touched on them in previous blogs. When dealing with these blogs, I am conscious that people have only 5 minutes for a quick read, but there are a few takeaways initially.
Nitec’s baseline policies far exceed the simple MFA required by Cyber Essentials, so implementing our baseline is a perfect step toward security.
Our baseline has been developed in line with Cyber Essentials, so if you implement the baseline, you will pass Cyber Essentials with flying colours. We can organise whatever you need, whether Cyber Essentials or the slightly more stringent “Cyber Essentials Plus” and penetration testing if required, so don’t hesitate to get in touch.
Most of the cost of security licensing is already held by most customers, so the prices of being secure are very low. Therefore, being secure is less a “profit and loss” item as much as it is a “hearts and minds” item. The ICO are aware of this and expects that you take security seriously.
Our customer portal allows you to see the extent to which you meet (or don’t meet) the requirements of Cyber Essentials in, more or less, real–time so you can be sure that you don’t just comply on the day of testing but all year round.
It seems such a waste to get a £98K fine and a considerable loss of reputation when the cost of achieving reasonable security is so reasonable. No?