We don't use buzzwords - we're just offering secure cloud solutions and the peace of mind that comes with them.
There is an almost constant stream of changes currently. Some IT people had assumed that the pace of change would decline over time, but alas, that has yet to be the case. Nevertheless, we need to face reality at some stage, so at Nitec, we are changing a few of our customer prerequisites.
Our new baselines:
1. Prerequisite for DPM Online backup.
2. Required Journey to Modern Authentication
Were you ever told you needed these?
Prerequisite for DPM Online Backup
Online backup has improved over the years, and now it's time to make this a prerequisite.
If your company has a fire, you can call the fire department, and they'll put it out. But what happens if you lose your data?
You'd think that companies would be willing to pay for insurance for their data. After all, it's as important to them as the building is to their business. But some companies never think of their data in terms of risk. Instead, they think of it as something that works every day without drawing any attention to itself.
In the event of a fire, some customers could recover more quickly with their data and no premises than with their premises and no data. Data is linked to everything, from what orders are currently open to who has paid for delivered goods. Even if production equipment has not been directly affected, you could struggle to run production if you can't work out your order book or purchase book.
Given the massive increase in ransomware over the last few years, it's never been more vital to have adequate recovery levels tested regularly. Most customers understand this, but we're no longer prepared to accept complacency. The bottom line is it's for your own good. We live in a world where every security expert says you must assume that hackers already have access to your network. Back-up would be a top priority in such a world.
Required Journey to Modern
Take the journey to modern. You won't regret it, and there are several reasons it is necessary. Reasons primarily based on the gradual retirement of On–Premises Policy Management through Active Directory Group policy in favour of In–Cloud Policy Management through Intune. "Sorry, what?" I hear you say. I know, it's borderline unintelligible! The bottom line is that there are fewer on–premises computers in your office than ever before. The policy is what controls and manages your computers, and it used to come from Active Directory on a Domain Controller in your office. Once a machine leaves the office, that control is almost entirely missing. It's not uncommon for some computers to have never been in the office.
This move to cloud management will be felt in many ways:
MFA and Compliant Devices
While Multi-Factor Authentication (MFA) is still valid and necessary, more is needed to ensure security. The reason is that social engineering has improved, and we have seen multiple cases of people having their MFA phished. Most staff are resistant to this, but there is a hard core of 20–25% of staff who are no match for some hackers. The latest compliant device policies add a third factor which causes minimal hassle for your staff members but add a significant load on a hacker.
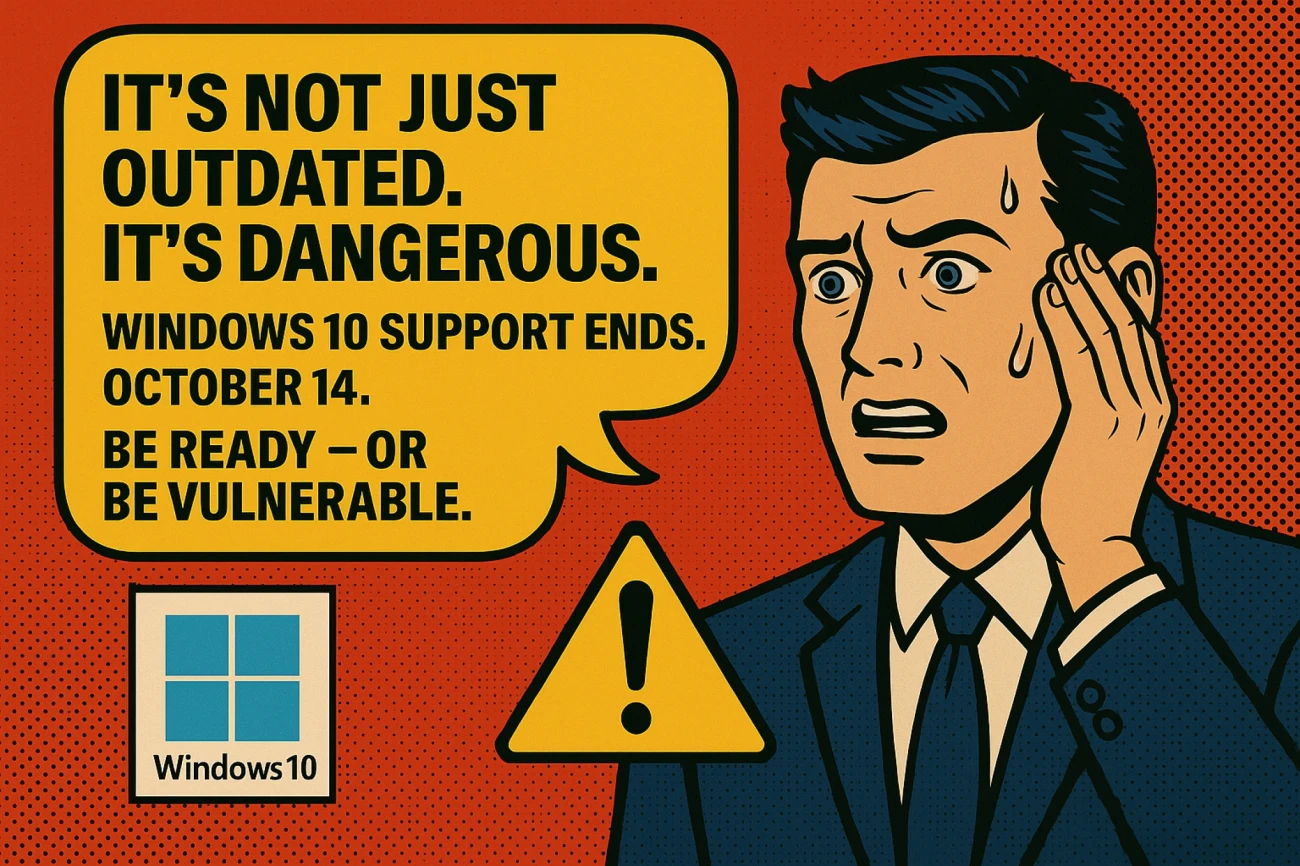
Update and Vulnerability Management
Keeping people out of your login is only half of the challenge. The other half is that software that hasn't been updated can often have some vulnerability that allows hackers to bypass the login security and get straight in. This is even more difficult in the modern era, where staff can literally be anywhere; at home, abroad and in the office. Microsoft has brought an element of control to this new update mechanism. It is hard to accomplish the required level of vulnerability management without Intune for any computers that do not live permanently in the office, without more expensive additional third–party applications. Most customers now have Microsoft 365 Business Premium, which has this vulnerability management, so expect to see this leveraged on your behalf very soon.
"Why would any hacker be interested in me?" I hear several of you say. Well, I'm glad you asked.
In truth, they're not targeting you. At least in the sense that they didn't wake up this morning and type "Small to Medium sized IT Companies in Antrim" into the search bar. It's more akin to people who break into cars in car parks. They are opportunists, and they take advantage of opportunities. If you routinely leave your handbag or wallet on the car's passenger seat, it's only a matter of time before an opportunity presents itself to an opportunist. However, Nitec suggests a simple process to avoid being targeted by such people: lock your car doors and put your valuables in the glove box or boot.