Most hacks occur because we are careless about these three things.
Prevention is better than cure. This concept is hardly alien to us in the environment we found ourselves in recently. The country was in the process of one of the most extensive preventative medicine experiments/projects (depending on your point of view) that the government has ever seen.
Things are similar in the world of IT. People are desperately trying to inoculate themselves to balance the harm from hackers by spending an amount of money commensurate with the expected potential damage. The question is: what is the correct spending level to keep yourself safe? This a topic for another blog.
Interesting as that question is, though, one of the things you can do to make life a great deal harder for hackers is to get your configuration right. These things cost very little, and while they won't all work for everyone, you can try them and reverse them quickly. Those who know our Nitec method will realise it's all about layers. We assume that each layer can be breached, but if you have a dozen layers, one of them will cause the hacker some significant issues, if not half of them.
Let's look at the 2021 HSE hack which took down public hospital systems in Ireland for somewhere between a week and a month, depending on the system concerned. Again, we see a prevalent attack path with several factors common amongst most of the hacks I have recently seen.
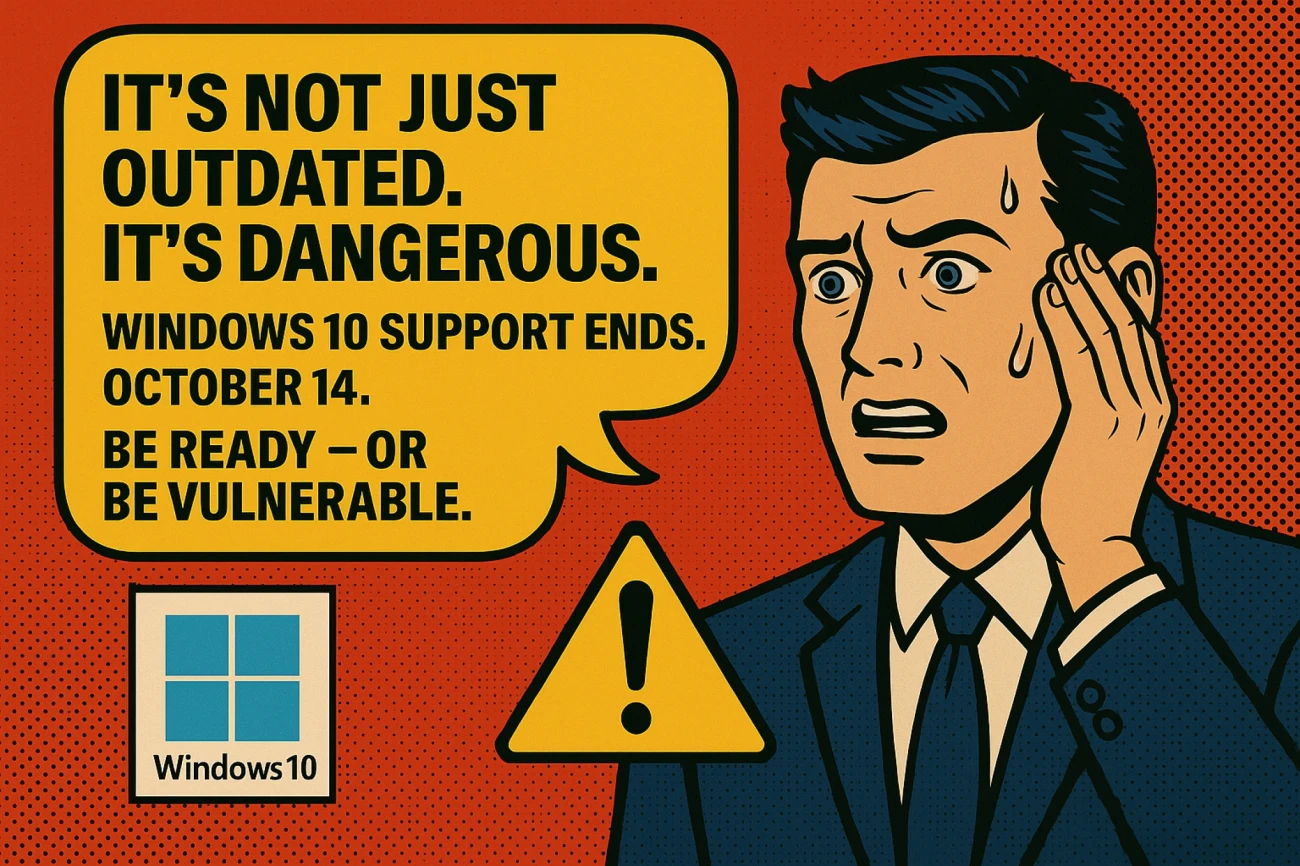
1. Poor patching/Old operating systems
2. Poor identity control – No MFA, no geo–blocking, no compliant devices.
3. Poor configuration.
We have talked about identity until you all are (and me) probably blue in the face, and the need to stay up to date. Surprisingly to almost no one, a lot of what we are discussing here does not work on Windows 7 (which stopped receiving security updates in January 2020 by the way). So, just to ram that home, if you are still using Windows 7, you need to get off it as soon as possible and to hell with the cost. I say that because you are comparing it to the price of a new desktop when you need to compare it to the cost of recovering your systems and repatriating your data (the toothpaste, in this example) into your control (the tube). While the cost of the PC is really defined (say £500 or £1000), the other is more ethereal. It might not be as intangible as you think. Hacks are becoming more common as each month passes. Studies show that around 236.1 million ransomware attacks occurred globally in just the first half of 2022. Let's face it. With those numbers, you wouldn't want to play Russian roulette, yet some of you are just mashing that trigger for all you're worth.
In this blog, though, we're looking at configuration.
Having your configuration right can place real barriers in the path of hackers. Many of the attacks go after your domain controllers, and although Microsoft has made some significant strides in this area, it is not something many appear to be aware of. If you get the domain, you have the kingdom's keys. Before I start, though, it's probably worth pointing out for clarity that the on–premises domain is on life support. It's like putting on a bit of lippy and sitting up in bed with the sheets hiding the IV. But make no mistake, all of the focus these days is on Azure Active Directory (AD), where security is in the prime of its youth, in my opinion. There are security methodologies in the cloud that don't work on AD. With that said, many of us will still have an on–premises AD, so we need to secure it.
Here's a short list of simple things you can do. We will revisit this again in the future I'm sure, but here's the starter.
Do you know precisely who has domain admin? I.e., is there an old account(s) you don't use anymore?
Are you sure the passwords can't be guessed? I recently met a customer, and their domain admin password was a thinly veiled version of their address. You absolutely should not do that. Please.
Have you placed them all in the protected user group? This forces better security on those accounts which makes stealing credentials harder.
Are you using reversible encryption? Hopefully not.
Have you protected your Local Security Authority?
Have you removed the use of built–in groups where possible?
Again, as we have explained in previous updates, we make it easy for you to see where your vulnerabilities are so that you can work through them. In addition, you can find your issues in the Nitec Customer Portal on a daily refresh cycle.
Get In Touch
If you've ever felt that your network was in chaos and you don't have the tools to bring some sense of order, then we'd like to speak with you about Nitec's IT management solutions. We can even help with deployment. Give us a call on 028 9442 7000 or email solutions@nitec.com.